What This Workflow Does
For IT, security, and DevOps teams, responding to alerts often starts with a simple question: "Where is this IP address coming from?" Manually looking up IP addresses across geolocation databases, threat feeds, and WHOIS records is a repetitive, time-consuming task that delays critical decisions. This automation solves that by creating a seamless bridge between your team's communication hub (Telegram) and powerful IP intelligence (Data24-7).
Every time an IP address is sent to your designated Telegram bot or chat, this Make.com workflow automatically triggers. It extracts the IP, queries the Data24-7 API for comprehensive details—including country, city, ISP, organization, and potential threat flags—and formats the results into a clear, immediate reply back in Telegram. This transforms raw data points into contextualized intelligence in under 10 seconds, empowering your team to assess risks, validate alerts, and take action without leaving their primary collaboration tool.
Pro tip: Use this not just for security alerts, but also for troubleshooting user login issues, analyzing website traffic sources mentioned in team chats, or quickly vetting IPs during vendor onboarding discussions.
How It Works
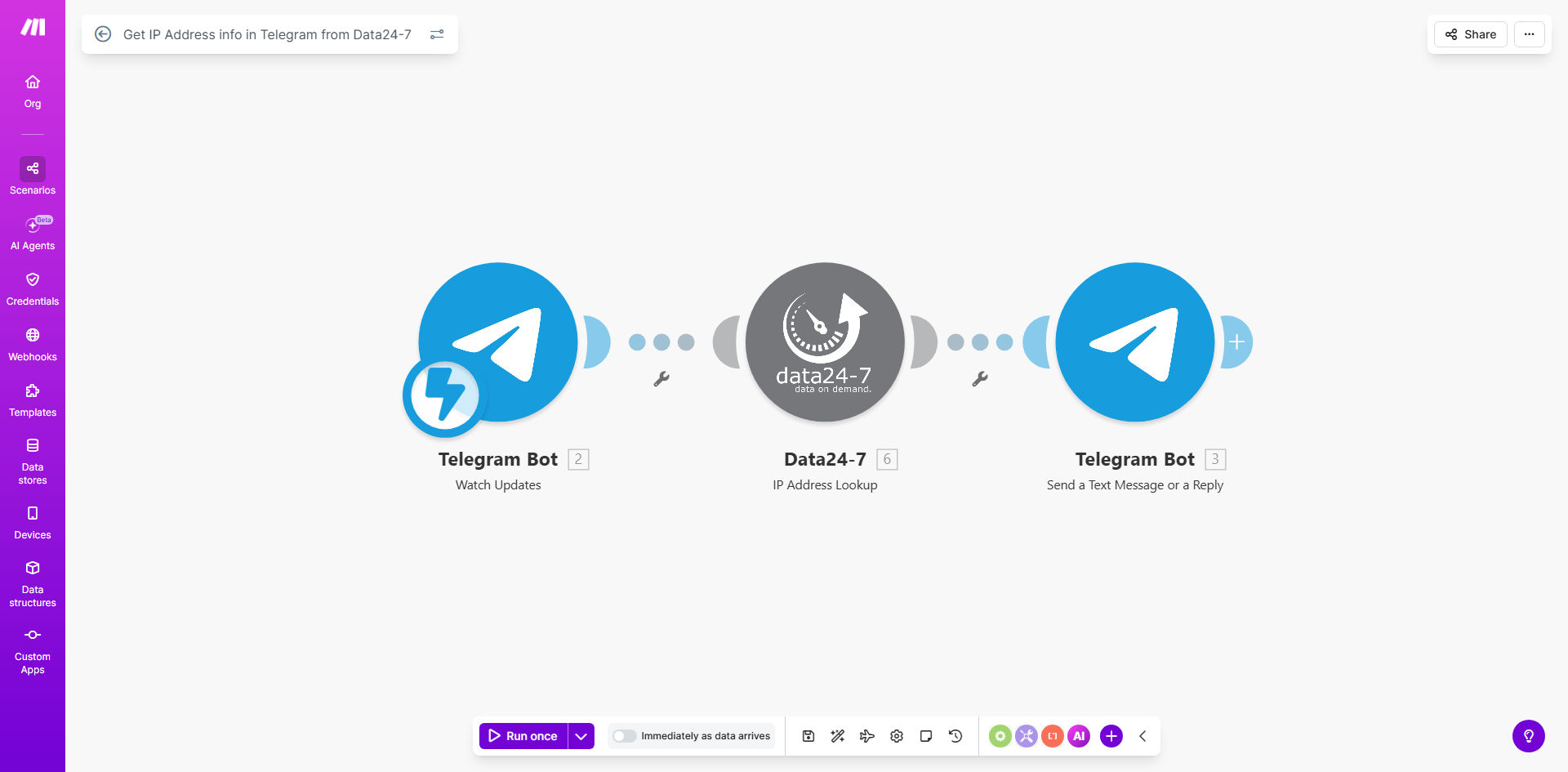
The workflow operates on a simple trigger-process-respond model, fully automated within Make.com's visual interface.
Step 1: Trigger from Telegram
The scenario monitors a specific Telegram bot or chat you configure. When a message containing an IP address (IPv4 or IPv6) is detected, it instantly captures the message content and the sender's details. The IP address is automatically parsed using a regex filter, ensuring only valid IPs proceed to the next step.
Step 2: Enrich with Data24-7
The parsed IP is sent as a query to the Data24-7 API. In a single call, it retrieves a rich dataset: precise geolocation (coordinates, city, region), network ownership (ISP, ASN, organization), connection type (mobile, corporate, hosting), and crucial security indicators like VPN, proxy, or Tor usage.
Step 3: Format & Deliver Intelligence
The raw API response is transformed into a human-readable summary. The workflow structures the key findings—highlighting location, ISP, and any threat flags—into a concise Telegram message. This formatted intelligence is then sent as a reply directly to the original chat, providing immediate context to the person who requested it.
Who This Is For
This template delivers immediate value to teams that handle digital operations, security, and support.
Security Operations Centers (SOCs) & IT Teams: Triage firewall alerts, failed login attempts, or suspicious activity logs discussed in team chats by instantly enriching IPs with threat data.
DevOps & Site Reliability Engineers: Quickly investigate the origin of anomalous server traffic or DDoS alerts mentioned during incident response calls in Telegram groups.
E-commerce & Fraud Prevention Teams: Assess the risk of customer orders or login attempts by checking if IPs are associated with VPNs or high-risk locations during manual review discussions.
Digital Agencies & Webmasters: Provide clients or team members with quick insights about website traffic sources or comment spam directly within project communication channels.
What You'll Need
- A Make.com Account: Free tier is sufficient to run this workflow.
- A Telegram Bot Token: Created via @BotFather on Telegram. This gives your workflow permission to read messages and send replies.
- A Data24-7 API Key: A subscription plan from Data24-7 to access their IP geolocation and threat intelligence API.
- A Dedicated Telegram Chat or Group: Where your team will send IPs for lookup. This could be a private group with the bot added or a direct message to the bot.
Quick Setup Guide
You can have this automation running in under 10 minutes.
- Clone the Template: Click "Get This Workflow" and clone it into your Make.com account.
- Connect Telegram: In the first module, add your Telegram connection using the bot token from @BotFather. Specify the chat or group to watch.
- Configure Data24-7: In the HTTP request module, insert your Data24-7 API key. The endpoint URL is pre-configured.
- Test the Flow: Send a test IP (like 8.8.8.8) to your Telegram chat. The workflow should run and return a detailed report within seconds.
- Activate & Deploy: Turn on the scenario in Make.com. It will now run automatically for every IP address received.
Key Benefits
Reduce incident response time from minutes to seconds. Security analysts no longer need to switch tabs, copy-paste IPs, and interpret raw API data. Context is delivered instantly where the discussion is happening, accelerating decision-making during critical events.
Eliminate manual, repetitive lookup tasks. This automation handles the grunt work, freeing up skilled team members for higher-value analysis and strategic security work. It's like having a dedicated research assistant for every IP address your team encounters.
Improve accuracy and consistency of intelligence. Manual lookups can lead to errors or missed data points. This workflow ensures every IP is checked against the same authoritative source (Data24-7) and that the full set of relevant data—geolocation, ISP, and threat flags—is always presented.
Create an auditable log of IP investigations. Every lookup triggered from Telegram is automatically logged within Make.com's history, creating a timestamped record of which IP was queried, by whom, and what the result was—valuable for compliance and post-incident reviews.
Foster collaborative security culture. By putting powerful intelligence directly into team chats, you democratize access to IP data. Everyone from junior analysts to managers can understand the context of alerts, leading to more informed discussions and shared responsibility for security.