What This Workflow Does
This automation solves a critical DevOps problem: securely backing up sensitive credentials from self-hosted n8n instances without manual intervention. When credentials are stored only within a Docker container, they become vulnerable to server failures, accidental deletions, or security incidents. Manual backup processes are often inconsistent, forgotten, or risky due to direct server access.
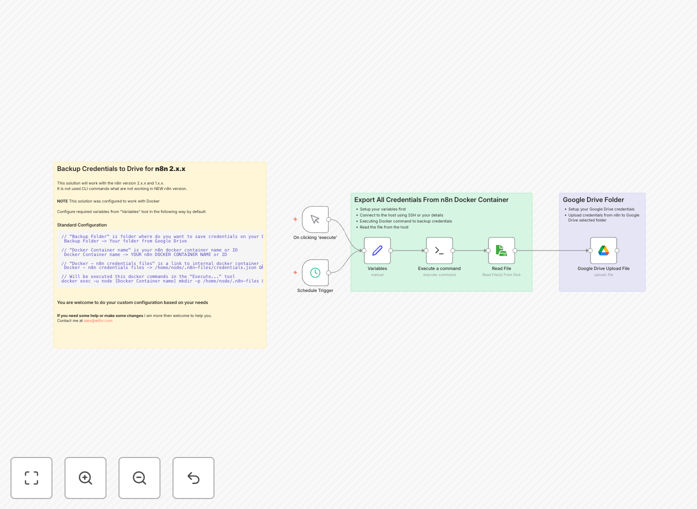
The workflow automatically connects via SSH to your host machine, executes the n8n export command inside the Docker container, retrieves the decrypted credential file, and uploads it to a designated Google Drive folder with a timestamp. This creates a secure, off-site backup history that enables quick restoration and meets compliance requirements for credential management.
How It Works
Step 1: Centralized Configuration
A variables node defines your Docker container name and file paths. This centralizes configuration, making the workflow adaptable to different environments by changing just one node.
Step 2: Secure SSH Execution
The workflow establishes an SSH connection to your host machine using key-based authentication. It executes the n8n export:credentials command inside the specified Docker container, generating a decrypted JSON file on the host filesystem.
Step 3: File Retrieval
The newly created credential file is read from the host filesystem via SSH. The workflow ensures the file exists and contains valid data before proceeding to upload.
Step 4: Cloud Upload with Timestamp
The credential file is uploaded to your Google Drive folder with a filename that includes the execution timestamp (e.g., n8n-credentials-2025-03-28.json). This creates versioned backups that can be tracked over time.
Pro tip: Configure the schedule trigger based on your credential change frequency. If you frequently add new integrations, set daily backups. For stable environments, weekly backups may suffice.
Who This Is For
This workflow is ideal for DevOps teams managing self-hosted n8n instances, IT administrators responsible for business automation security, and companies requiring compliance with data protection regulations. It's particularly valuable for:
- Teams using n8n for critical business processes where credential loss would cause operational disruption
- Organizations needing demonstrable backup procedures for audit compliance (ISO 27001, SOC 2)
- Companies with multiple n8n instances requiring consistent backup policies
- Businesses transitioning from manual backup processes to automated, reliable systems
What You'll Need
- A self-hosted n8n instance running in Docker (version 2.x.x or later)
- SSH access to the host machine with key-based authentication configured
- A Google Drive account with API access enabled
- Basic familiarity with n8n workflow import and node configuration
- A designated Google Drive folder for credential backups
Quick Setup Guide
- Import the template: Download the JSON file and import it into your n8n instance.
- Configure variables: Open the Variables node and enter your Docker container name (typically
n8n). - Set up SSH connection: In the Execute Command node, add your host IP, username, and SSH key/password.
- Authenticate Google Drive: Connect the Google Drive Upload node with your account credentials.
- Select backup folder: Choose the specific Google Drive folder where backups should be saved.
- Adjust schedule: Modify the Schedule Trigger node to your preferred backup frequency.
- Test execution: Run the workflow once manually to verify all connections work correctly.
Key Benefits
Eliminates manual backup risks: Human error, forgotten backups, and inconsistent procedures are replaced by automated, scheduled execution. This ensures credentials are backed up reliably regardless of team workload or attention.
Provides geographic redundancy: Storing credentials in Google Drive creates off-site backups that survive local hardware failures. Cloud storage offers version history and access controls unavailable with local storage solutions.
Enables quick disaster recovery: When credentials are lost due to server issues, the latest backup can be restored within minutes rather than requiring days to manually re-establish every integration connection.
Supports compliance requirements: Automated backups with timestamps and audit logs help meet data protection regulations requiring secure credential storage and demonstrable recovery capabilities.
Reduces security exposure: SSH automation eliminates the need for human intervention on production servers, minimizing attack vectors while ensuring consistent, logged execution.